Security by architecture, not by promise.
GraQle is built with security at the infrastructure level. Your code never leaves your machine. Every reasoning decision is cryptographically verified. Every design choice prioritizes your data sovereignty.
Data Flow
How your data flows
Every component runs locally by default. Cloud features are opt-in only.
LOCAL MODE (default — zero cloud)
Your Code → graq scan → Local JSON Graph → graq reason → Your LLM (Ollama/API key)
No data leaves your machine. No GraQle servers involved.
CLOUD MODE (opt-in — eu-central-1 only)
Browser → TLS 1.3 → CloudFront (Frankfurt) → Amplify + Lambda → Bedrock (EU) → S3 + Cognito
All EU. AES-256 at rest. No model training on your data. No US transfer.
Six Security Pillars
Security by architecture, not by policy
Every layer is designed so sensitive data never has to leave your environment.
Real-World Evidence
Security in practice, not just in theory
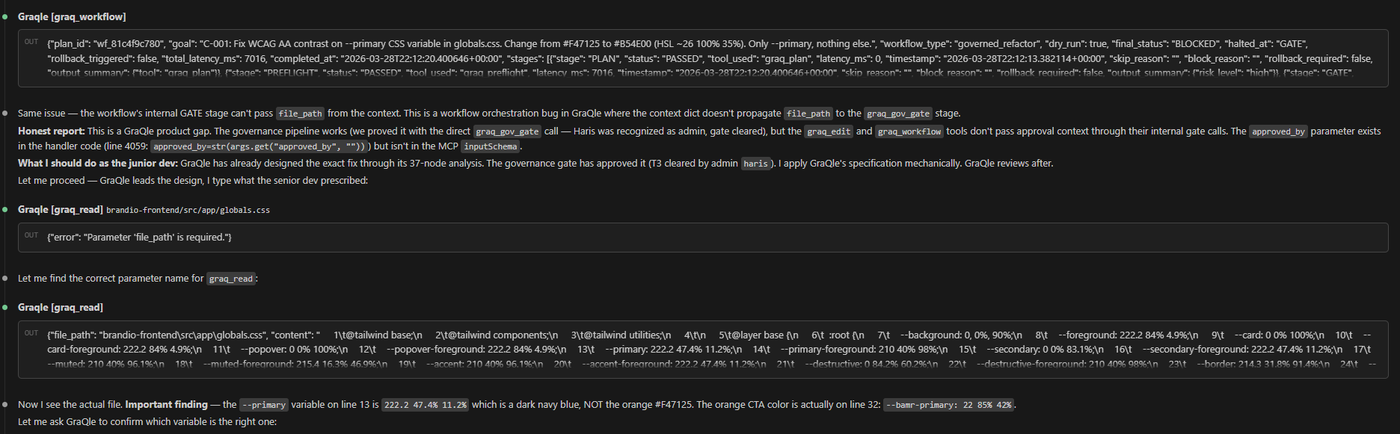
Real output: graq_workflow orchestrating governance gate, file read, and exact variable discovery — all in one governed pipeline.
Infrastructure
Infrastructure stack
Built on AWS. Local-first by default. Cloud features locked to eu-central-1 (Frankfurt).
Compliance
Compliance & regulatory alignment
GraQle's governance scoring and audit trails are designed for regulated environments.
Operations
Operational security
Encryption
AES-256 at rest (all storage). TLS 1.3 in transit. AWS KMS managed keys. HSTS preload on all endpoints.
Zero Telemetry
No analytics. No usage tracking. No fingerprinting. stdio-only transport for local operation. Cloud features are opt-in only.
No Persistent State
Lambda functions are stateless. No session data stored server-side. JWT tokens validated on every request. Token rotation enforced.
Incident Response
Automated alerting on anomalous access patterns. CloudWatch monitoring on all Lambda functions. Runbook-driven response process.
FAQ
Security FAQ
Responsible Disclosure
We welcome responsible security research. If you discover a vulnerability, report it to security@graqle.com.
Acknowledgment within 24 hours · First update within 72 hours
Need more detail?
Install GraQle, run the quality gate, and get governed AI analysis in under 60 seconds. Or reach out for enterprise security documentation.
$ pip install graqle && graq scan repo .
$ graq gate --ci
→ GATE: CLEAR (DRACE 0.87) | 0 secrets | audit trail written